Testing to see if this works. Sometimes installing Ubuntu in a PC without 3D capable video hardware results in a non-bootable system: rather it boots but you can’t see anything, and since the default configuration is that OpenSSH-server is not installed, you can’t shell into it either. You can’t even use CTRL-ALT-F2 to change TTYs…
Protecting Your Web Site from Loss of Business
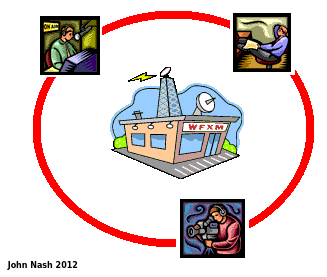
The Godaddy DNS outage was caused by internal error, not a hack. We should specify name lookup via more than one DNS company so that if one company is unavailable, the other will still work and access to our web sites will be unaffected by a single point failure.
VMWare Player and Ubuntu
VMWare has a habitual problem with NOT being usable in Ubuntu until several months after a release. I found a fix here: http://askubuntu.com/questions/130937/how-do-i-install-vmware-player-4-0-3. The bottom line is here: I based this on the instructions I found here: vmware player compile issue. To boil it down to the simplest steps: Download this tarball: http://weltall.heliohost.org/wordpress/wp-content/uploads/2012/01/vmware802fixlinux320.tar.gz Extract the…
Mainstream Tablet Prices Dropping to $149
I have said for some time the primary and secondary price points for the glut of tablets that will become available this fall will be $149 and $249 with a distant tertiary point at $400. Here is another manufacturer who is adjusting their SRP to become salable. There is nothing wrong with the Nook Color:…
Microsoft on target this time
Refer to http://www.infoworld.com/d/the-industry-standard/microsoft-surface-fuels-fear-and-loathing-in-pc-land-199671 Microsoft is moving forward with it’s Surface series of tablets, which will change with the way businesses are already changing: in other words, I feel that Microsoft is getting back in touch with reality and adapting. However, most other manufacturers are refusing to change, which is likely to kill them. This is the same hubris…